You can grant users access to the Services tab. By default, new users have no permissions.
Grant Access by using the UI
Prerequisite:
- A DC/OS user account without the
dcos:superuserpermission.
-
Log into the DC/OS GUI as a user with the
dcos:superuserpermission.
Figure 1. DC/OS UI login
-
Select Organization and choose Users or Groups.
-
Select the name of the user or group to grant the permission to.
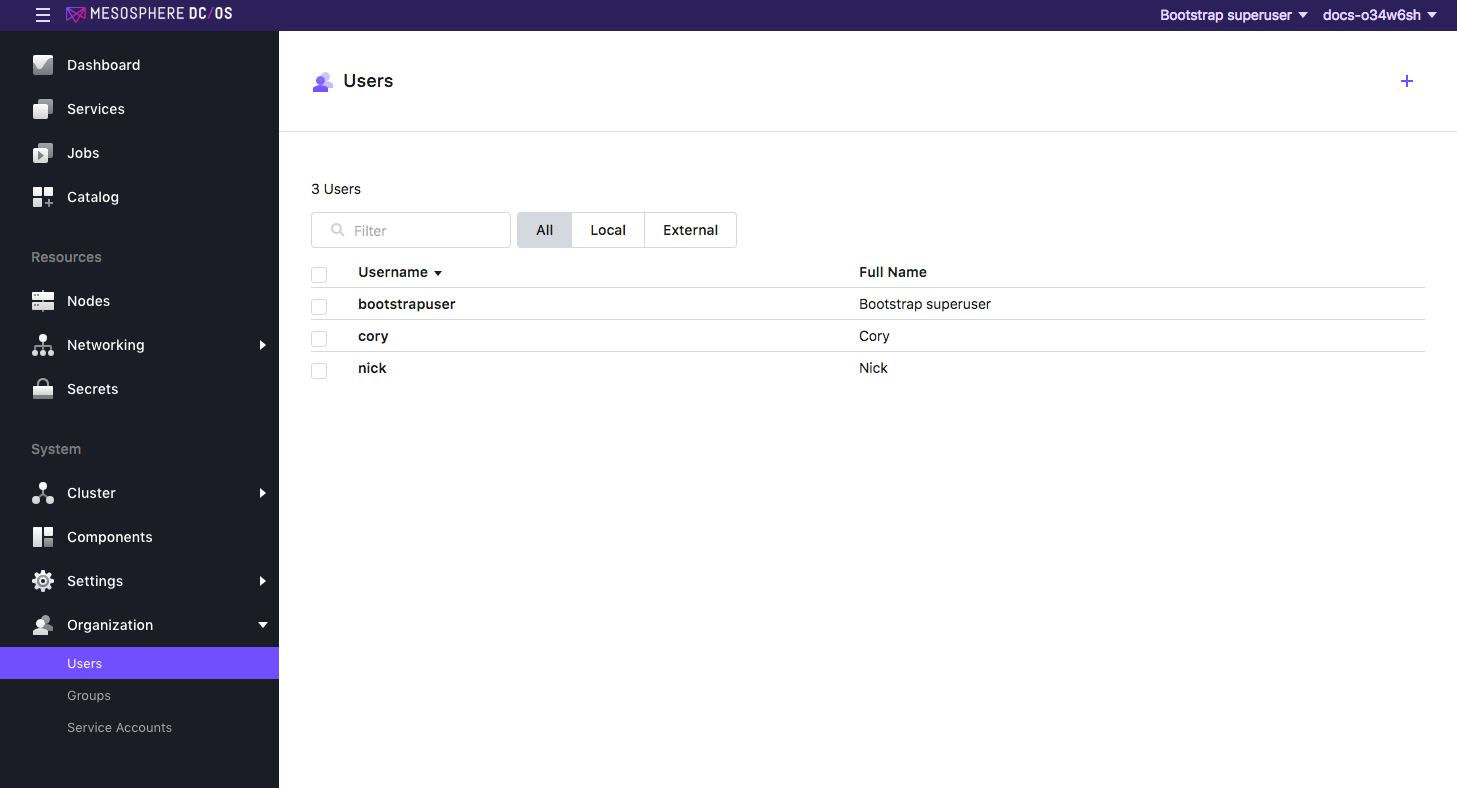
Figure 2. Select user or group to grant permissions to
-
From the Permissions tab, click ADD PERMISSION.
-
Click INSERT PERMISSION STRING to toggle the dialog.
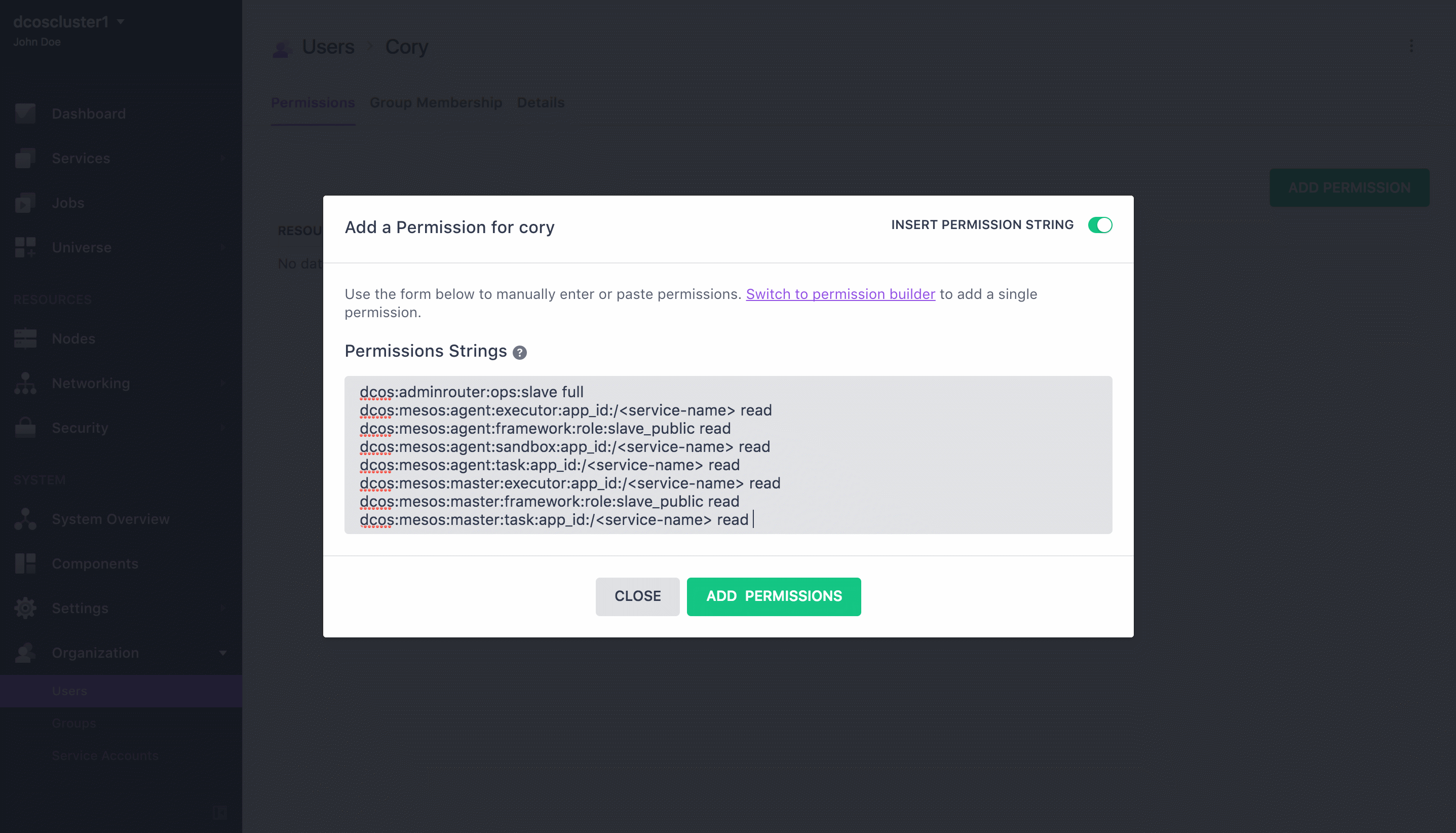
Figure 3. Insert Permission String
-
Copy and paste the permission in the Permissions Strings field. Choose the permission strings based on your security mode and click ADD PERMISSIONS and then Close.
Permissive
Services tab
dcos:adminrouter:service:marathon full
dcos:service:marathon:marathon:services:/ full
Services tasks
dcos:adminrouter:ops:mesos full
Task details and logs
dcos:adminrouter:ops:slave full
Strict
Services tab
dcos:adminrouter:service:marathon full
dcos:service:marathon:marathon:services:/ full
Services tasks
dcos:adminrouter:ops:mesos full
Task details and logs
dcos:adminrouter:ops:slave full
dcos:mesos:master:framework:role:slave_public read
dcos:mesos:master:executor:app_id read
dcos:mesos:master:task:app_id read
dcos:mesos:agent:framework:role:slave_public read
dcos:mesos:agent:executor:app_id read
dcos:mesos:agent:task:app_id read
dcos:mesos:agent:sandbox:app_id read
Granting Access by using the API
Prerequisites:
- You must have the DC/OS CLI installed and be logged in as a superuser.
- You must get the root cert before issuing the curl commands in this section.
Tips:
- Service resources often include
/characters that must be replaced with%252Fin curl requests, as shown in the examples below. - When using the API to manage permissions, you must create the permission before granting it. If the permission already exists, the API will return an informative message and you can continue to assign the permission.
Permissive
Grant access to DC/OS Services tab
-
Create the permission.
curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:service:marathon \ -d '{"description":"Grants access to the Services tab"}' -
Grant the following privileges to the user
uid.curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:service:marathon/users/<uid>/full
Grant access to DC/OS services task details and logs
-
Create the permission.
curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:ops:mesos \ -d '{"description":"Grants access to the Mesos master API/UI and task details"}' curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:ops:slave \ -d '{"description":"Grants access to the Mesos agent API/UI and task details such as logs"}' -
Grant the following privileges to the user
uid.curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:ops:mesos/users/<uid>/full curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:ops:slave/users/<uid>/full
Grant access to all services in the Services tab
-
Create the permission.
curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:service:marathon:marathon:services:%252F \ -d '{"description":"Grants access to all services"}' -
Grant the following privileges to the user
uid.curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:service:marathon:marathon:services:%252F/users/<uid>/full
Strict
Grant access to DC/OS Services tab
-
Create the permission.
curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:service:marathon \ -d '{"description":"Grants access to the Services tab"}' -
Grant the following privileges to the user
uid.curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:service:marathon/users/<uid>/full
Grant access to DC/OS services task details and logs
-
Create the permission.
curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:ops:mesos \ -d '{"description":"Grants access to the Mesos master API/UI and task details"}' curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:ops:slave \ -d '{"description":"Grants access to the Mesos agent API/UI and task details such as logs"}' curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:master:framework:role:slave_public \ -d '{"description":"Grants access to register as or view Mesos master information about frameworks registered with the slave_public role"}' curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:master:executor:app_id \ -d '{"description":"Grants access to all executors on the Mesos master"}' curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:master:task:app_id \ -d '{"description":"Grants access to all tasks on the Mesos master"}' curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:agent:framework:role:slave_public \ -d '{"description":"Grants access to view Mesos agent information about frameworks registered with the slave_public role"}' curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:agent:executor:app_id \ -d '{"description":"Grants access to all executors running on the Mesos agent"}' curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:agent:task:app_id \ -d '{"description":"Grants access to all tasks running on the Mesos agent"}' curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:agent:sandbox:app_id \ -d '{"description":"Grants access to the sandboxes on the Mesos agent"}' -
Grant the following privileges to the user
uid.curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:ops:mesos/users/<uid>/full curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:adminrouter:ops:slave/users/<uid>/full curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:master:framework:role:slave_public/users/<uid>/read curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:master:executor:app_id/users/<uid>/read curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:master:task:app_id/users/<uid>/read curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:agent:framework:role:slave_public/users/<uid>/read curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:agent:executor:app_id/users/<uid>/read curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:agent:task:app_id/users/<uid>/read curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:mesos:agent:sandbox:app_id/users/<uid>/read
Grant access to all services in the Services tab
-
Create the permission.
curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ -H 'Content-Type: application/json' \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:service:marathon:marathon:services:%252F \ -d '{"description":"Grants access to all services"}' -
Grant the following privileges to the user
uid.curl -X PUT --cacert dcos-ca.crt -H "Authorization: token=$(dcos config show core.dcos_acs_token)" \ $(dcos config show core.dcos_url)/acs/api/v1/acls/dcos:service:marathon:marathon:services:%252F/users/<uid>/full
 DC/OS Documentation
DC/OS Documentation